Unravelling the mobile security
conundrum
What do you look for in a mobile phone? As well as the ability to
make calls - and no-one really cares about that - the modern smartphone hosts a
standard feature set: email, a web browser and multimedia capability.
Screen size, storage and connectivity may change depending on how
much you want to spend. Then it’s a question of platform: some prefer Apple’s
slick but locked-down environment, with its curated book of apps; others are
more at home in Android’s rough-and-ready world. Windows is a must for a chunk
of the population, and many mobile emailers remain addicted to BlackBerry.
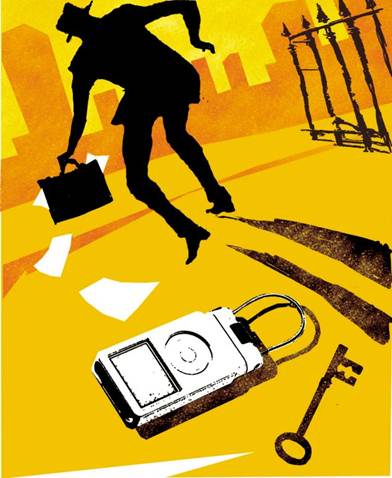
What is less often considered by consumers is how secure a
smartphone is. And yet, even more than a PC, your handset offers up the keys to
your email, bank account and all manner of personal data. If you want to steal
someone’s ID, you’ll need little more than their phone.
It’s a conundrum plenty of businesses face every day. How do you
give your staff mobile access to email and productivity tools, without opening
the door to hackers?
Ever wondered why so many enterprises run BlackBerry phones? It’s
simple: RIM BlackBerry Enterprise Server software is a tool that allows the
network administrator to remotely run a secure fleet of phones. If a BlackBerry
is mislaid, it can be bricked and wiped by tech support. And updates can be
rolled out fleetwide.
A CEO may think it’d be cool for all staff to have Phones, while
the finance director thinks Android is a better idea - but the network admin is
a BlackBerry fan with a soft spot for Windows. I guarantee it.
Trouble is, it’s a decision that’s almost immaterial. Give someone
a locked down BlackBerry, and they’ll turn up at work with two phones: one for
work, one for pleasure. Short of putting in metal detectors and relieving
staffers of their gadgets at the door, you can’t stop people bringing in phones
of all flavours - each one a potential Trojan horse, capable of bringing
malware in and taking data out.
Mobile computing is a fact of life, and it’s not going away.
Neither are the risks, nor try as you might you can’t remove them all. The only
safe phone is one that’s never used. But the risks can be managed.
Whether used principally for business or pleasure, every mobile
device should run security software. But unlike in the Windows world, the
principle reason is not to fend off maiware. Indeed, research by AV-Test
suggests Android antivirus doesn’t work (tinyurl.com/73tjd2n). The data
gathered will help security vendors get a handle on the threat dynamic, but
mobile antivirus is no panacea.
Much more important is the ability to remotely locate, lock and
wipe your mobile device. The best mobile security solutions do exactly that.
Norton Mobile Security, for instance, offers a web interface where you can find
out where your phone is. Then, if it is in the hands of a crook, you can make
it emit a loud scream, take a photo of the miscreant, track its location, wipe
all the data and lock out prying eyes. Other tools offer similar functions. Use
them, and you may lose your handset, but not your valuable data. And just as
every Windows user should have antivirus, antispyware and a firewall, no mobile
device should be left unprotected.