A single line of code on a linked
website could reset a device. ‘What were Samsung smoking?’ tweeted engineer Pau
Oliva
Smartphones based on Google’s Android
operating system, including Samsung’s flagship Galaxy S III, are vulnerable to
having data remotely wiped without the user’s consent, security experts have
discovered. Ravi Borgaonkar, a researcher in the Security in Communications
department at the Technical University of Berlin, took the stage at a security
conference last month to demonstrate how opening links received via QR codes, a
handset’s built-in NFC payment chip or push SMS messages could result in the
remote wiping and resetting of a Galaxy S III.
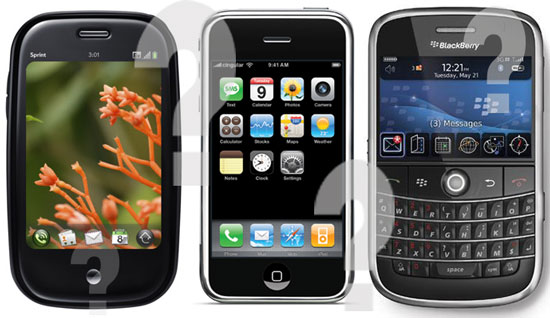
Smartphones
based on Google’s Android operating system
The vulnerability, said Borgaonker, is down
to the way the S III uses Unstructured Supplementary Service Data (USSD). USSD
is used to send messages between a phone and an application server. Embedding a
single line of code in a frame on a website, claimed telecoms engineer Pau
Oliva, could cause vulnerable devices which arrive at the web page via an
automated link from QR, NFC or push SMS to implement a factory reset without
any further user input.
Devices that arrive at the same web page by
browsing in a web browser are not affected. ‘What were Samsung engineers
smoking when they set a USSD code to do a factory reset?’ tweeted Oliva.
Borgaonkar said other Android phones,
including the HTC One series, Sensation and Sensation XL, Sony Ericsson’s
Xperia series and some Motorola Droids could also be affected if they haven’t
been updated since June. Samsung quickly issued an over-the-air security update
for the S III.
‘We would like to assure our customers that
the recent security issue concerning the Galaxy S III has already been resolved
through a software update,’ said a spokes-person, urging all Galaxy S III
owners to download the fix.
THE VULNERABILITY highlights a growing problem. Smartphones are becoming at least as
important to people as their personal computers, but the Android platform in
particular has attracted a growing number of malware attacks, according to a
report earlier this year from Finnish computer security firm F-Secure. In that
report, F-Secure said that it had discovered 37 new variants of Android
malware, nearly four times as many as a year previously. More alarmingly, the
number of malicious Android application package files had risen from 139 in
2011 to 3,063 in 2012.
Many of those files arrive in ‘Trojan
horses’ masquerading as popular apps. One example is a bootleg copy of Angry
Birds which contained a piece of malware. When the game was downloaded, it ran
as normal, meaning the malware often went undetected.

One
example is a bootleg copy of Angry Birds which contained a piece of malware
The F-Secure report noted: ‘In Q1 2012,
malware authors are focusing on improving their malware’s techniques in evading
detection, as well as exploring new infection methods…Android threats have
continued to improve their techniques, yet nothing much has changed in their
operation in collecting profit. The majority of malware discovered in Android
markets are SMS-sending malware that reap profit from sending messages to
premium numbers.’
Most of the infected apps are downloaded
from third party stores, said F-Secure, but some have found their way on to
Google Play, the official Android app store.
A recent report from another security
software vendor, McAfee, estimated that mobile malware had risen by 700% in a year
and that 85% of it was on the Android platform. Users of Apple’s iOS can’t
install apps from sources other than the official App Store, so the
opportunities for malicious executable code to find its way into devices are
much more limited than with Android, which is marketed as an open system.
Earlier this year, in response to growing
concerns over security threats to Android, Google introduced a tool called
Bouncer to scan apps made available on Google Play for malware. But two
security researchers discovered in June that it could be tricked fairly easily
into passing malicious apps. And it doesn’t run at all on third party stores
such as Amazon’s App Store.
ANDROID IS POPULAR with malware writers for two reasons: it’s used by a huge number of
people and it’s easier to attack than its main competitor, iOS. But is iOS
immune from malware? The common perception is that Apple’s careful vetting of
every app will protect users from infection, but security software maker Eugene
Kaspersky doesn’t think so.

Find
and Call grabbed contact details from users’ iPhones without their permission
and sent SMS messages to those contacts’ mobile phones inviting the recipients
to try out the app
Like other security app vendors, Kasper-sky
has something of an axe to grind: Apple’s iOS software development kit (SDK)
doesn’t permit the kind of low-level system access that they would need to
write anti-virus software for the platform, so they’re effectively locked out
of iOS. Kaspersky told tech website The Register earlier this year: ‘It is much
more difficult to infect iOS but it is possible, and when it happens it will be
the worst-case scenario because there will be no protection.’ The
counter-argument is that the whole way Apple operates iOS constitutes better
protection than users of open platforms could ever get from third party
software.
One app that did slip past Apple’s vetting
process earlier this year was Find and Call, which grabbed contact details from
users’ iPhones without their permission and sent SMS messages to those
contacts’ mobile phones inviting the recipients to try out the app. No damage
or loss was caused and the app was removed.
Apple has made several recent improvements
to privacy and security in iOS 6. A new Privacy tab in Settings lists all the
apps that have requested access to your Contacts, Calendar, Bluetooth sharing,
Location Services and more. And, crucially, it allows you to revoke permission
at the flip of a slider. iOS 6 also prevents app developers from accessing
unique device identifiers, known as UDIDs. These alphanumeric codes allow each
iPhone or iPad to be tracked and, although primarily used for benign purposes,
offered an opportunity for intrusion into users’ privacy.
None of this will be of much help to iOS
owners who bypass Apple’s protections by ‘jailbreaking’ their devices.
Jailbroken iPhones can run apps downloaded from any source, without Apple’s
permission, which thousands of users seem to think is a risk worth taking. In
2010, some jailbroken iPhones were infected with a worm known as Ikee. This
directed customers of ING Bank to a fake site which harvested their usernames
and passwords. Tim Armstrong, a researcher for Kaspersky in the US, said at the
time: ‘We only saw those problems on jailbroken iPhones.’
Security threats don’t always come as
malware, of course. In a one-off attack, journalist Mat Honan had his iOS
devices wiped by someone who’d gained access to his iCloud account. The hacker
was able to do this using social engineering that is, tricking privileged users
into security mistakes – to exploit a flaw in systems at Apple and Amazon. In
short, the last four digits on a credit card, which Apple considered secure
enough to use as verbal proof of ID, were displayed unencrypted by Amazon.
Using those four digits from Honan’s card, the hacker got his iCloud password
from Apple support and was then able to use Find My iPhone to wipe Honan’s
phone and other devices. Apple has since changed its systems.
There’s broad consensus among security
experts that iOS 6 made significant improvements to an OS that was already very
secure. That doesn’t mean users should be entirely complacent, and simple
phishing attacks, such as emails asking users to input details into fake
websites, can strike on any system. For now, however, it’s Android that
provides a cautionary tale for other platforms.